- Цена
- 25-200
- Контакты
- https://stealseek.io/contact.html
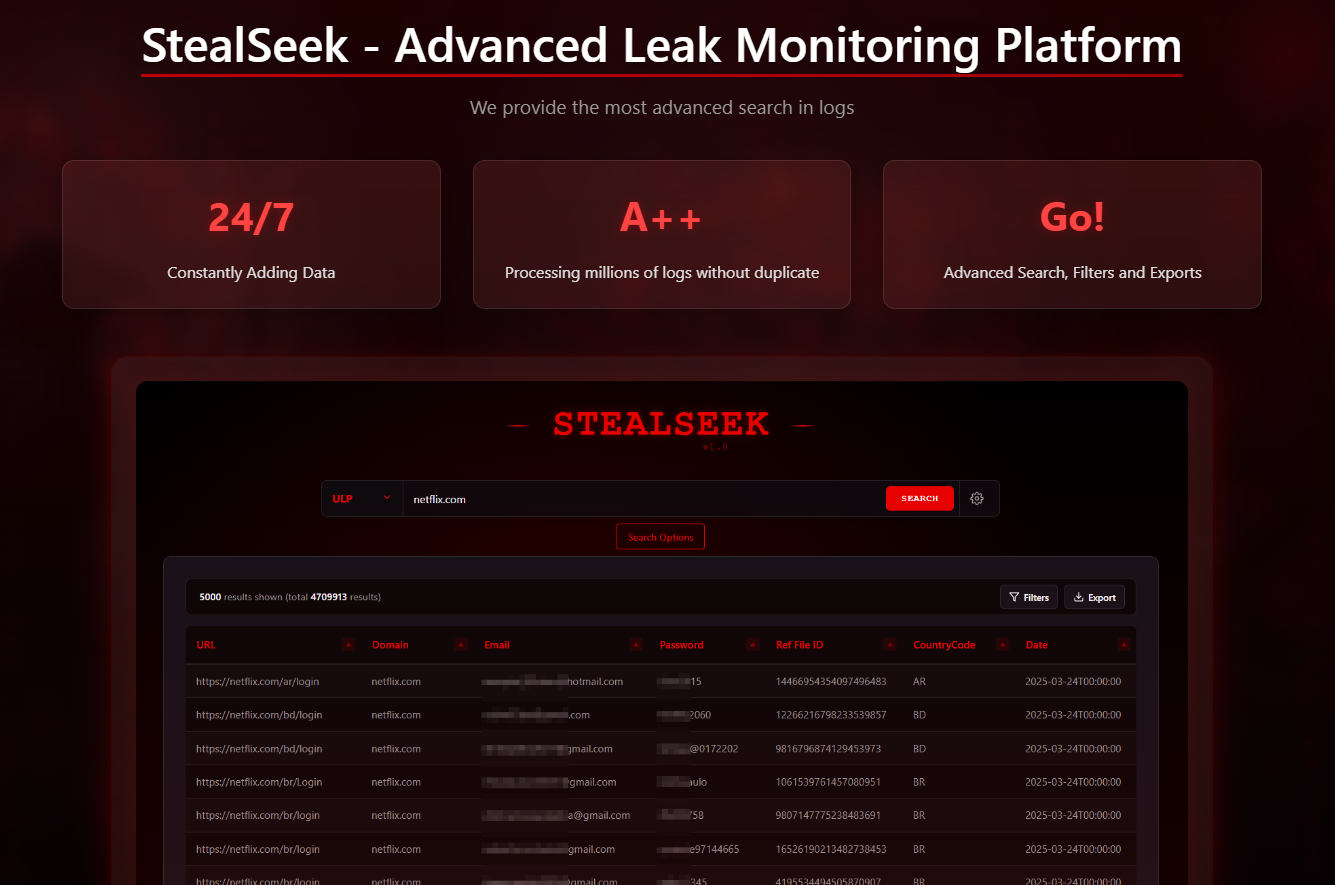
What is StealSeek?
StealSeek is a next-gen OSINT & breach intelligence platform designed for cybersecurity experts, red teamers, analysts, and osint enthusiasts.
Instead of processing plain txt ULP like others or pulling ready-made APIs from other services, StealSeek processes full stealer logs, credentials, cookies, autofills, ULPs, and much more.
We’ve evolved from a simple Telegram bot into a complete web-based search engine and leak monitoring platform.
Accessible via web interface — no setup required.
---
Search Like a Pro

Our search engine gives you:
Fast, column-based queries
Support for emails, domains, passwords, HWIDs, usernames, etc.
"Partial Match", time filters, total count & pagination
Export results to .CSV, .TXT, .JSON
Advanced panel lets you refine down to the last log.
---
Log Viewer & Downloads

For stealer logs, you can:
View log details by category (ULP, Autofills, Cookies, etc.)
Search within logs
Download full original logs (.zip)
Every action is one right-click away.
---
Real-Time Leak Monitoring

Setup alarms for:
- Emails
- Domains
- Full Domains
- Computer Names
- HWIDs
- IP addresses
- Client/User data
---
Subscription Plans (Monthly)
Standard: $69/month
Professional: $119/month
Business: $199/month
Want to test first? Try our weekly plans at lower prices!
API access is sold separately. Contact us to enable API for your project or dashboard.
View Pricing & Credits
---
Contact Us
Email:
support@stealseek.io — Support Requests admin@stealseek.io — General / Sales
Telegram:
- @StealSeek — Official Channel
- @stealsek_bot — Support Bot
- @Stealseek_admin - Telegram support
- stealseek.01 - Signal support
Session ID:
05fadfaf60927b3d13d6152688cbdfddedf5fbb7508468cbf378973a9c4dcb590b
Use PGP or Session for sensitive communication.
---
Why Choose StealSeek?
Billions of real records
Most advanced search table structure
Powerful filtering and advanced search options
Multiple result display & visualization controls
Inspect and download the full raw log files (stealer logs included)
Real-time alerting & asset monitoring
Verified, high-quality logs — no junk or noise
Uniquely sourced data — includes exclusive, unreleased leaks
Reliable, low false-positive infrastructure
Privacy-first platform — no tracking, no logging, full user confidentiality
Web-based, zero setup — no tool installation required
Trusted by DFIR, red teams, researchers, and threat hunters
"Not just data — intelligence."
USER GUIDE
Последнее редактирование: